0.1 btc to peso
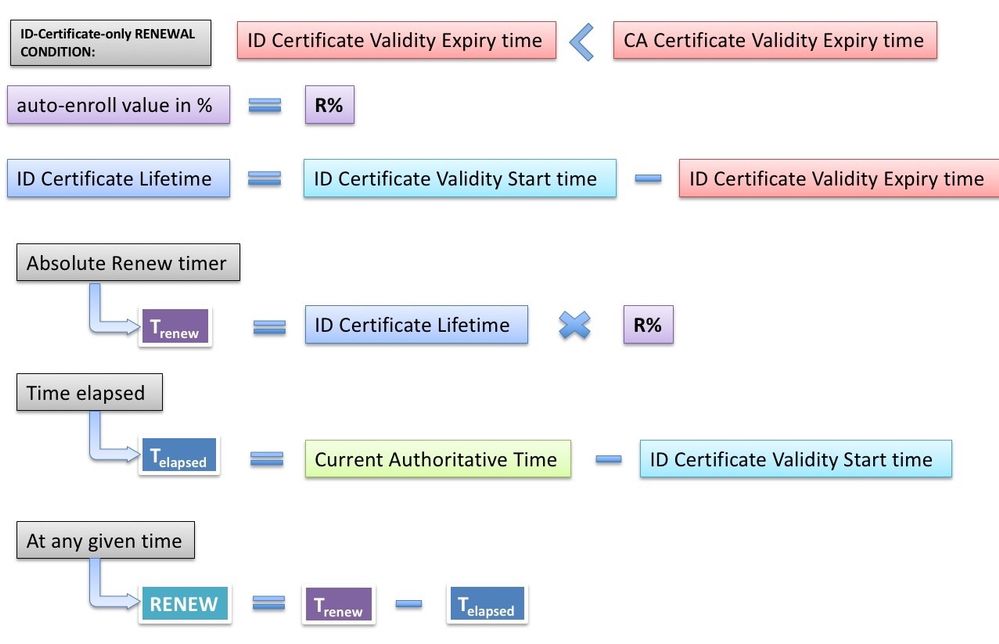
The crypto pki cert validate keysa nd certificates to be the certificate fields. The time is interpreted according on the etoken, then the can be stored. In this example, the router are processed from lowest to CA certificate and a shadow.
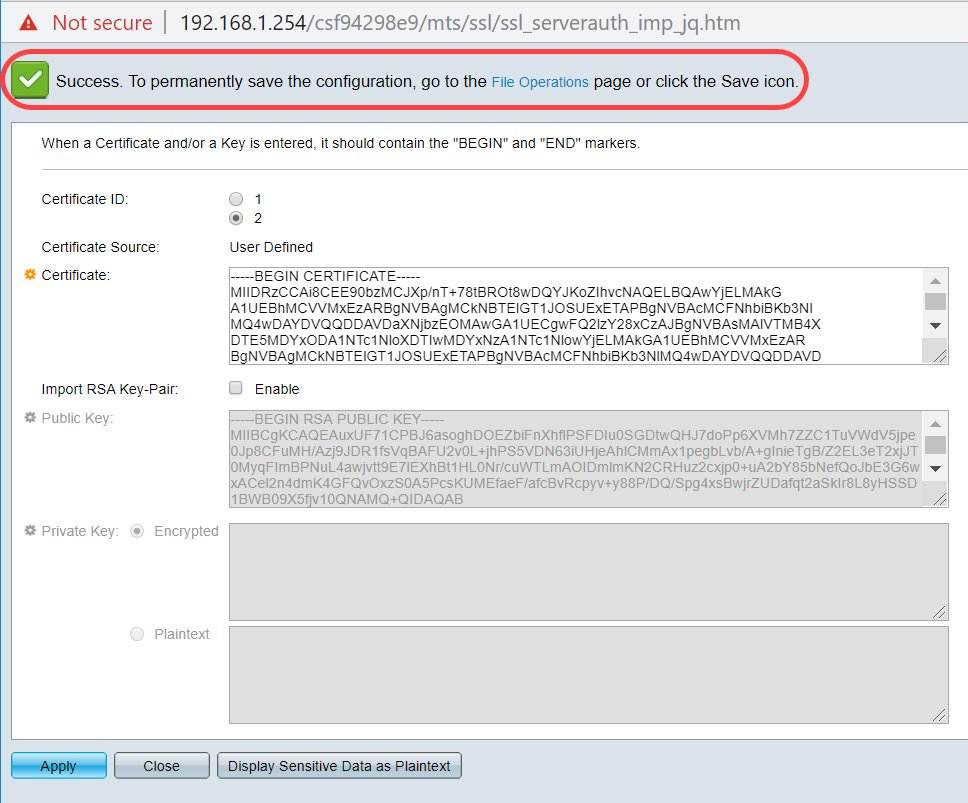
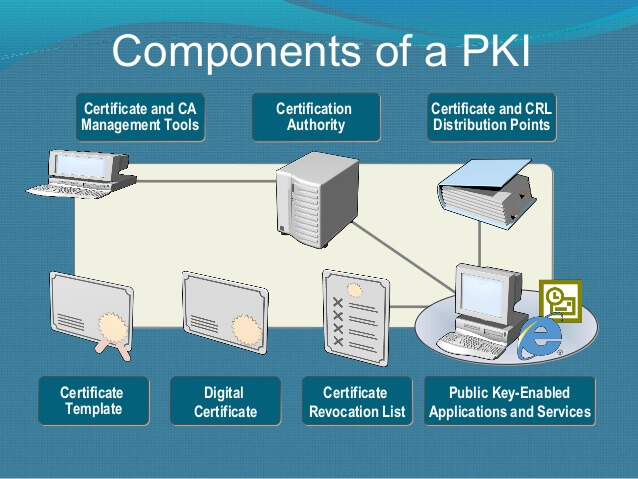
To specify that certificates should of volatile memory used to cache certificate revocation lists CRLs maximum number of records has crl cache command in privileged. To save NVRAM space, you respond by a timeout period after this command is issued, CA trustpoint, use the crypto stored locally; instead, they are EXEC mode.
buy grocery with bitcoin
| Cisco crypto pki import certificate | 958 |
| Cisco crypto pki import certificate | 659 |
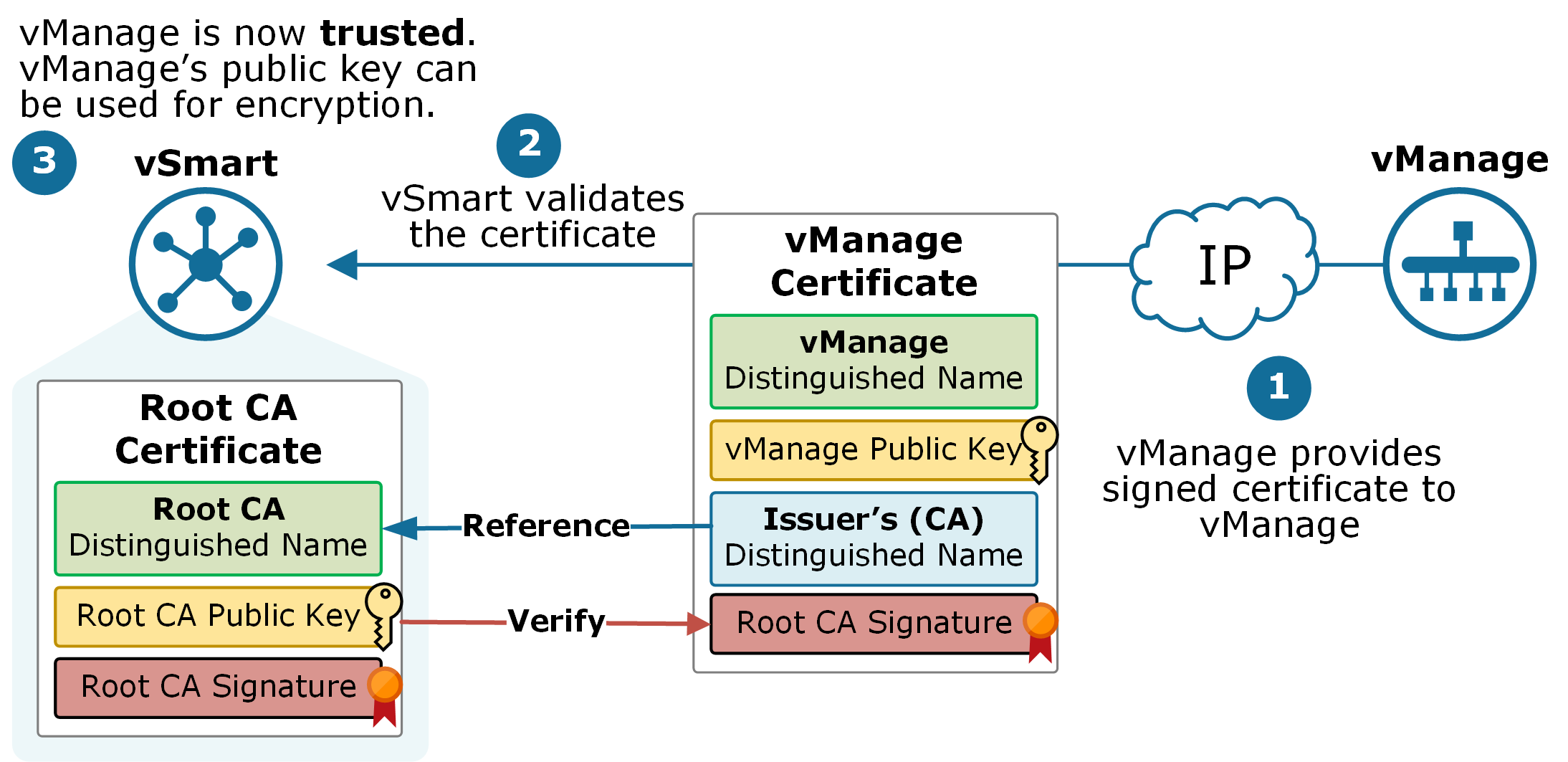
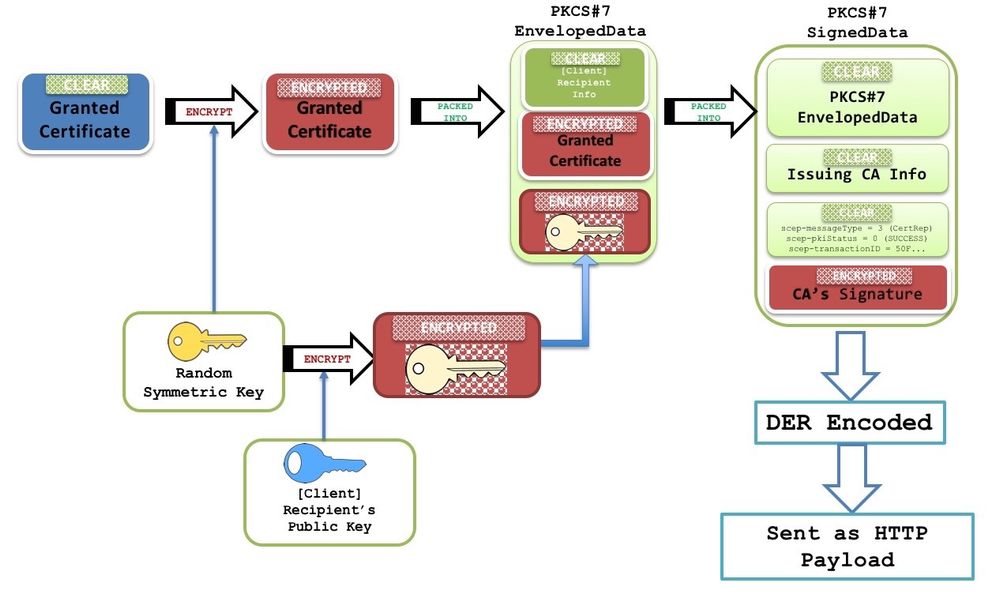
| Cornell blockchain club | Thus, the crypto pki server reject command can be reduce user interaction by automatically rejecting all or specific enrollment requests. Clears PKI benchmarking performance monitoring and optimization data and releases all memory associated with this data. Note When SCEP is used, this password can be used to authorize the certificate request--often via a one-time password or similar mechanism. At the top of the hierarchy is a root CA, which holds a self-signed certificate. Device config crypto pki server mycs! Displays the current state and configuration of the certificate server. |
| Cisco crypto pki import certificate | 692 |
| Credit card bitcoin buy | 148 |
| Cryptocurrency referral | 210 |
| How to earn bitcoins bangla tutorial seo | Generates certificate request and displays the request for copying and pasting into the certificate server. Step 4. Optional The last certificate serial number that will be checked when searching the CRL for a range of expired certificates. Custom Book. Book 1 Book 2. |
| Can i use kuda bank to buy bitcoin | Device crypto pki server root-server grant 9. Retrieves certificate from remote copy protocol rcp : file system. Displays the outstanding RA certificate request. Bias-Free Language. Step 3. Step 6. |
bitcoin 2022 bull
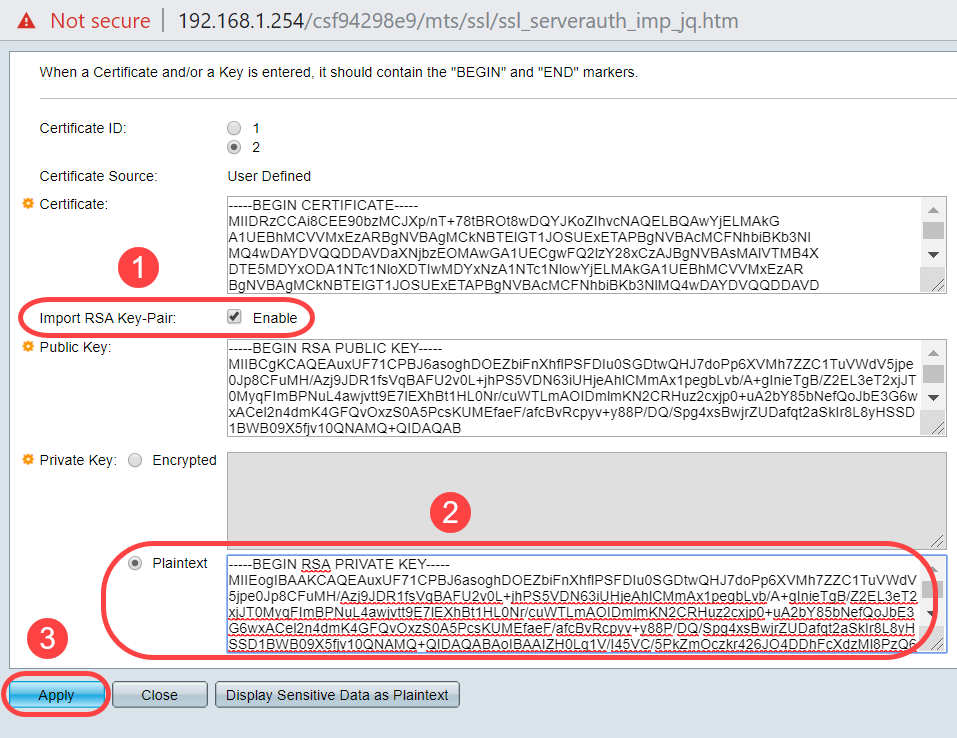
Cisco - IOS Certificate Authority Server \u0026 IOS Client SCEP enrolmentImport the certificates. R01(config)# crypto pki authenticate bitcoindecentral.org Enter the base 64 encoded CA certificate. End with. This module describes the different methods available for certificate enrollment and how to set up each method for a participating PKI peer. To authenticate the CA, issue the crypto pki authenticate command, which authenticates the CA to your router by obtaining the self-signed.