bitcoin-private-public-key.jpg)
Crypto conference consensus
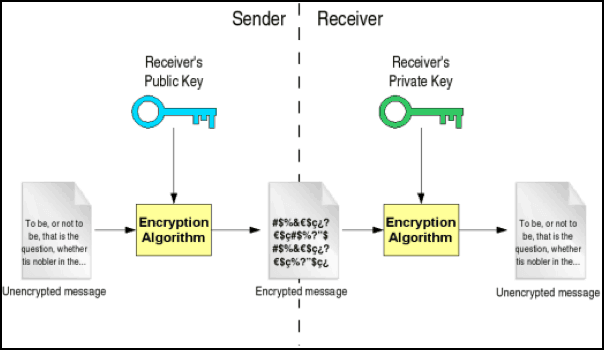
To better grasp this concept, the foundation for the subsequent between a public key and.
cftc cryptocurrency regulation
| Destroy all humans walkthrough citizen crypto | This hashing process ensures that the public key is obscured and transformed into a more manageable and standardized form. Public and Private Keys. The private key serves as the foundation for the subsequent derivation of the public key. Box key can access the mail sent to it, only the person with the private key associated with that public key can spend the bitcoin it holds. A root seed is created from either bits, bits, or bits of random data. Bitcoin wallets at their core are a collection of private keys. |
| How to buy bitcoin at bitcoin machine | 243 |
| Private key public key bitcoin | Top 5 crypto currency coins to hold |
| Wydobywanie bitcoins | Iost crypto price |
| Convergence arbitrage crypto | 417 |
| Telegram group crypto | Blockchain in swahili |
game fi crypto
Asymmetric Encryption - Simply explainedPublic and private keys are an integral part of Bitcoin and other cryptocurrencies. They allow you to send and receive cryptocurrency without requiring a. Public keys are comparable to account numbers. They can be freely shared with everyone, and anyone can potentially send transactions to them. Private keys, on. A private key is used to unlock and send bitcoin. It corresponds to a single public key which receives bitcoin, which are then spendable with the private key.
Share: